FBPC 1.0.3 is released
A new version of Performance Comparer for Firebird (FBPC) is now available. Version 1.0.3 has the following changes:
- Fixed some parameters data type identifying logic (the traceapi writes the params data types based on their internal field type, not the declared type)
- The statement’s grid wasn’t showing a value when the statement execution time was below 1ms
- Added some error handling during the statements execution
- Now any errors during the execution of an statement will be logged in the errors.log file (in the application directory)
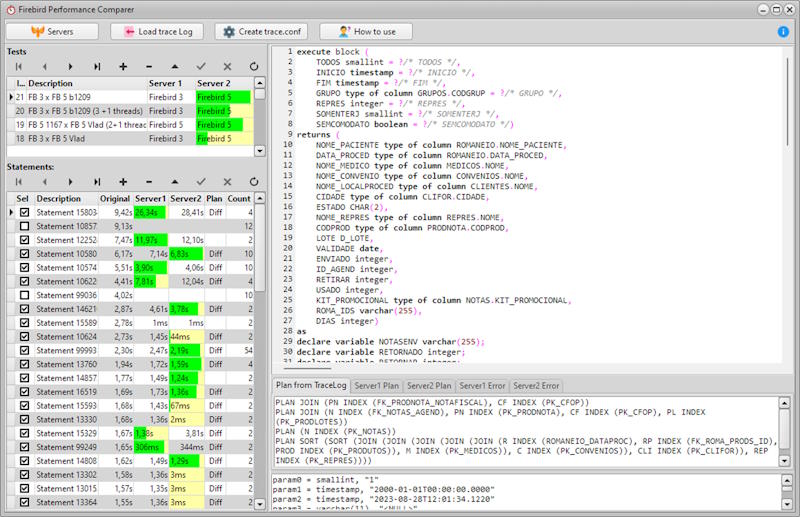
FBPC is a free tool that can help people to compare the performance of real life SQL statements between two Firebird versions, or even between the same Firebird version but with different configurations in firebird.conf.